Microsoft Theme Sharing Vulnerability Could Result In Password Theft
The ability to share themes gives attackers the option of stealing access data from Windows 10 users. The way it works can be compared to the well-known phishing attacks in emails.
Windows 10 offers its users the possibility to share their own theme with all individual settings with other users. If you right-click on the currently active appearance in the theme’s settings, you are offered the option of saving it and then passing it on to other users. The configuration file, in which the various options are recorded, can, however, be fatally manipulated. Like the US magazine Bleeping Computer
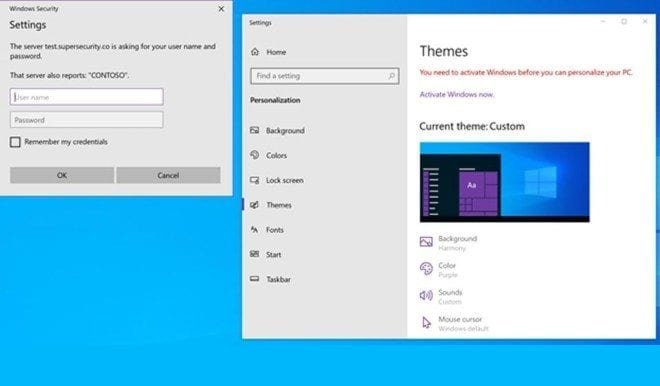
citing the security researcher Jimmy Bayne reports, a background image can be set here that should only be downloaded from an external SMB address. In this case, the user who wants to install the theme will be asked to log in. The corresponding request gives the impression that your own access data is required for the Windows account.
Entire Microsoft account affected
When the user enters this, the identifier is transmitted to the server of the theme provider – the password is in the form of a hash, but it is not generated with a highly complex algorithm. In particular, simpler passwords, such as those used by many users, can be reconstructed in a fairly manageable amount of time.
And that can have serious consequences – because the login ID applies to the entire Microsoft account of the user. Attackers can then log into e-mail accounts, Azure accounts, and company networks with knowledge of the password. It is not to be expected that Microsoft will change anything since it is essentially a properly functioning feature that can only be misused. Users should therefore be careful here. And administrators in company environments would do well to adopt the so-called NTLM guidelines and to prevent any data transfer to external servers.
Digital marketing enthusiast and industry professional in Digital technologies, Technology News, Mobile phones, software, gadgets with vast experience in the tech industry, I have a keen interest in technology, News breaking.